
 DP Solutions has been ranked the 74th top Cloud Services Provider in the world on MSP Mentor’s Talkin’ Cloud 100. DP Solutions is one of just three companies in the State of Maryland to make the list!
DP Solutions has been ranked the 74th top Cloud Services Provider in the world on MSP Mentor’s Talkin’ Cloud 100. DP Solutions is one of just three companies in the State of Maryland to make the list!
The Talkin’ Cloud 100 recognizes the top 100 Cloud Services Providers (CSP’s) from around the world and all they do to help customers manage, provision and support their cloud technologies to meet their business objectives.
To learn more, or see the complete list, visit www.talkincloud.com.
You can defend your data with all the latest and best technology. But if just one team member gets tricked into giving away the keys to the castle, it’s game over. Hackers know this. And that's why so many use social engineering to break in.
And it’s not just the big companies you hear about on the news. On February 3, 2016 a suspect posing as the CEO of Magnolia Health Corp. obtained a spreadsheet with sensitive data about their employees. On February 23, someone posing as an employee of Central Concrete Supply Company obtained confidential W2 records and disappeared with them.
In a 2011 survey, Check Point Software Technologies found that nearly half of the companies surveyed reported one or more social engineering attacks resulting in losses ranging anywhere from $25,000 to $100,000 per occurrence.
Unfortunately, there just aren’t any whiz-bang tricks or tools that will automatically prevent a clever "social engineer" (SE) from breaking in. The keys to protection are awareness and vigilance. To help you know what to watch for, here are five common ploys - and how to deflect them:
1. Familiarity - In this type of scheme, the hacker becomes familiar to an employee. Social networking sites can reveal an employee’s schedule and favorite hangouts. The hacker might then frequent the same bar or restaurant. After a drink or two, some key fact may slip out... The best way to bust this ploy is to be careful to not get lulled into a false sense of security around people you haven’t thoroughly vetted.
2. The Consultant - A social engineer poses as a consultant for hire. Once they get the gig they can scoop up all the info they need from you and your team because of their seeming authority. Watch for this especially with IT consultants. Do NOT trust blindly. Vet every consultant, and never give all the keys to the kingdom. Just because someone has the skills to fix your server or network doesn’t mean they won’t steal your data. Vet thoroughly, and, as Ronald Reagan said, ‘trust but verify’.
3. Piggybacking - The SE waits by a secured door for someone to use their passcode and enters right behind them. Or the SE struggles with a heavy box and asks a legit employee to hold the door open for them. Being kind and helpful, the employee helps the SE right into the building… free to do as they please. To foil this one, never forget the dangers of allowing a stranger in without proper clearance.
4. The Interview - Key information often escapes during interviews. A smart social engineer will gain an interview and deftly pick up all the information they need to hack into your network. Make sure any data provided during an interview offers nothing in the way of secrets. Keep the conversation light, or even superficial to avoid leaking critical data.
5. Angry Man - You may have seen this on TV… Somebody has an angry tone on the phone, or is grumbling to themselves as if they’ve just had an argument. We all tend to avoid people like that. Enough people avoid them and the way is cleared into the heart of the company - and your data. Don’t go along with it. When you see this exploit unfolding, call security.
The key to preventing social engineering attacks is a well-trained workforce. You and your people may be your company’s greatest asset. Yet without regular, proper training, human beings can be the weakest link in your company’s data defenses.
How you can protect your network from a costly cyber attack
As a fellow business owner, I’d like you to take advantage of my extensive research and experience in protecting data networks for small and medium companies. Our business owner’s guide, The Top 10 Ways Hackers Get Around Your Firewall And Anti-Virus To Rob You Blind steps you through 10 ways to protect your company from the coming deluge of cyber attacks we can expect over the next several years and beyond.
To get your FREE copy, visit www.dpsolutions.com/hackers.
Mark Sanborn
“My kids are natural multi-taskers!” a friend exclaimed. She bragged that they could listen to music, watch TV and do their homework all at the same time. She might have been proud of their efforts, but she wasn’t accurate about their abilities. Research has concluded that it will take her kids longer to do their homework and likely they won’t do it
as well.
We think of multitasking as the ability to successfully perform more than one activity at the same time. It has become a seemingly ubiquitous phenomenon like walking in the park while talking to a friend. But there is a difference: walking doesn’t require our cognitive attention, so we are free to concentrate on our conversation. Other situations are more complex. For instance, it’s a different matter to read a book and listen to
a lecture.
In reality, what we commonly refer to as multitasking is the rapid shifting of attention from one task to another that creates the illusion we are performing them concurrently.
Nancy K. Napier Ph.D., in her article, The Myth of Multitasking said, “…much recent neuroscience research tells us that the brain doesn’t do tasks simultaneously, as we thought (hoped) it might. In fact, we just switch tasks quickly. This rapid switching of tasks makes us prone to error and ends up consuming more time than if we undertook one task at a time.
Workplace demands often create the perceived need to continually switch tasks. That makes people less effective. The ability to do a thing well and quickly requires full attention, and the myth of multitasking prevents that from occurring.
Success in any area is a function of the capacity to pay attention. Isaac Newton, for example, credited his success and discoveries as “owing more to patient attention than to any other talent.”
So what can you do? Here are some suggestions:
Stop fooling yourself. You’re not truly multi-tasking, you’re task switching. And that’s fine if that’s what you want to do. But there is a better way.
Block uninterrupted time to work on important projects. Aim for at least 30-60 minutes without phone calls, walk-ins or other distractions.
Choose to focus your attention on one thing at a time. For example, at your next meeting, try listening to others rather than glancing at your smartphone or jotting unrelated notes.
Give people your undivided attention. While it sounds cliche, it is difficult to do, but the payoffs are big. Not only will you improve the interaction, but you’ll demonstrate the regard you have for the other person.
Consciously avoid demanding others to multi-task. Don’t interrupt a colleague involved in another activity to make a request. Pick (or schedule) times to interact when the other person isn’t distracted by competing demands.
Read Cal Newport’s book, Deep Work. It is one of the best books I’ve read in recent years and will provide many insights and tactics you can use to beat the myth of multitasking.
|
Mark Sanborn, CSP, CPAE, is president of Sanborn & Associates, Inc., an idea studio dedicated to developing leaders in business and in life. Mark is an international best-selling author and noted authority on leadership, team-building, customer service and change. Mark is the author of eight books, including the best seller The Fred Factor: How Passion in Your Work and Life Can Turn the Ordinary into the Extraordinary, which has sold more than 1.6 million copies internationally. Learn more about Mark at www.marksanborn.com
|

Download this Free Business Owners Guide and discover how to protect your company from the flood of cyber attacks we can expect over the next several years and beyond.
 |
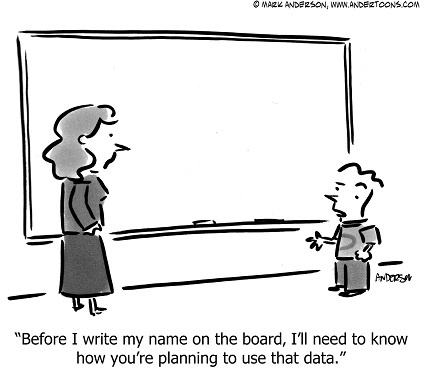
Important! We hate spam as much (or more!) than you and promise to NEVER rent, share, or abuse your e-mail address and contact information in any way. |

Brothers Services provides five-star remodeling, roofing, and exterior contracting services throughout the state of Maryland. From kitchens and bathrooms, to decks, chimneys, skylights, and everything in between, Brothers Services has all your contracting needs covered. Brothers uses quality materials and its workers are qualified, well-trained, and well-supervised. The company is committed to integrity and honesty and will always provide you with excellent value and the best possible solution at a fair price.
Brothers Services has been a fully managed IT services client since 2013. With Managed IT Services, the organization enjoys peace-of-mind knowing that their technology needs are being proactively addressed and monitored so they don’t have to worry about IT issues on a daily basis. Additionally, with a widely mobile staff, Brothers has implemented Microsoft Office365 to ensure employees can access the information they need from anywhere at any time and remain productive.
Brothers invites you to visit their Home Design Showroom in Timonium or their Remodeling Design Center in Columbia. For more information, visit www.brothersservices.com.

During the month of October we are holding a special “refer a friend” event.
Simply refer any company with 10 or more computers to our office and once we’ve completed our initial appointment with your referral, we’ll rush you a $50 Gift Card as a thank-you. Your referral is under no obligation to use our services. We also promise to be 100% respectful of their time.
Fill out our referral form or email us at sales@dpsolutions.com with your referral’s name and contact information today!