
Celebrating Women in IT
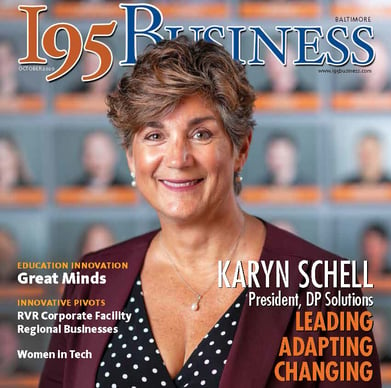
DP Solutions' President Karyn Schell
makes the cover of i95 Business Magazine
See the full article on the
The #1 Mistake Your Employees Are Making Today That Lets Cybercriminals Into Your Network
We all make mistakes. It’s a fact of life. But as we all know, some mistakes can have serious and lasting consequences – especially when it comes to business, cyber security and the constant cyberthreats that are out there.
While some businesses have invested heavily in cyber security, many have not. When it comes to network and data security, one of the most vulnerable areas of the economy is small businesses.
More often than not, small businesses simply don’t go all-in when it comes to IT security. Some fear they don’t have the budget and worry that IT security is too expensive. Others don’t take it seriously – they have an “it will never happen to me” attitude. Then there are those who invest in some security, but it’s limited and still leaves them vulnerable in the long run.
But there is one area of IT security where every business is vulnerable. You can have the greatest malware protection in the world and still fall victim due to this one big mistake.
Your employees lack IT security training.
It’s as simple as that. When your team isn’t trained on IT or network security and they aren’t aware of today’s best practices, you open yourself to major risk. Here’s why: We make mistakes.
Scammers and cybercriminals have the most success when they are able to trick people or play on the emotions of their victims. One common emotion they use is fear.
No one likes to get a message telling them that their bank account has been compromised. This is how phishing e-mails work. The scammer sends an e-mail disguised as a message from a bank or financial institution. They may tell your employee that their account has been hacked or their password needs to be changed immediately. They use fear to trick them into clicking the link in the e-mail.
So, concerned about their bank account, your employee clicks the link. It takes them to a web page where they can enter their username, password and other credentials. Sometimes it even asks for their full Social Security number. (Scammers are bold, but people fall for it!)
As you guessed, the web page is fake. The link in the e-mail directs your employee to a page that allows the scammer to collect their data. Some thieves use it to access their bank account, but others sell the information for a quick buck. No matter the situation, the information has fallen into the hands of crooks.
The challenge is that phishing e-mails have gotten harder to spot. Scammers can spoof legitimate web addresses. They can make fake e-mails look like the real deal. But there are still plenty of minor details that indicate the e-mail is a fake.
This is one of the MANY reasons why comprehensive employee IT training is so important. Training helps employees identify red flags. But more than that, it helps them identify changing red flags. For instance, a phishing e-mail from 2010 looks nothing like a phishing e-mail from 2020. Scammers stay ahead of the curve. They know the trends, and they know how to adapt. Your employees also need to know the trends and need to be ready to adapt.
Good IT training covers much more than phishing e-mails. It helps your employees identify security red flags across the board.
These include:
Good training is also continuous. Cyber security training isn’t a one-and-done deal. It’s something you do every quarter or twice a year. Just as you keep your business’s equipment maintained, you have to keep your employees’ cyber security knowledge maintained. After all, your employees are your first defense against outside cyber-attackers. When they know what they’re dealing with, they’re better equipped to stop it in its tracks and protect your business.
The bottom line is that a lack of training is the biggest threat against your computer network and the health of your business. You need to have a strong training program in place to make sure your employees stay up-to-date. But you don’t have to do it yourself. We can help. Along with your team, let’s protect your business together.
What Makes a Leader Successful Today?
Intentionality and the 3 Shifts
Mark Sanbron
Have you ever wondered what one thing all successful leaders have in common? First, consider what all unsuccessful leaders have in common: they lack focus.
Either they aren’t clear on what they’re trying to do or they know what they need to do but aren’t doing the right things to achieve their objectives. Both waste money and resources and leave organizations stuck in the status quo.
This affects leaders regardless of the size or type of organization, and that’s why I wrote The Intention Imperative: 3 Essential Changes That Will Make You A Successful Leader Today.
What all great leaders have in common is intentionality— being crystal clear on what you’re trying to achieve and taking the right actions every day to achieve it.
Why do many business leaders lack clarity?
What are the symptoms and signs of a leader who lacks clarity?
In my book, I explain intentionality and then share what I believe are imperative changes leaders need to take today to succeed: the shift from structure to culture, from motivation to inspiration and from experience to emotion.
Imperative 1 – Culture
“Culture is what we think and believe, which then determines what we do and what we accomplish.”
In The Intention Imperative, I teach the five levers you have for creating and maintaining the culture you desire. Creating it is the job of a leader.
Imperative 2 – Inspiration
“Inspiration doesn’t have to be mysterious or complicated to create.”
What is inspiration? It is motivation to the power of purpose. It is linking meaning to motives. Inspiration doesn’t come from outside force or artificial causes. It develops from the work itself and how the leader is able to demonstrate importance and impact.
Imperative 3 – Emotion
“Emotions are everywhere and they are the single biggest factor in how we make decisions.”
A negative emotional experience can be offset with a positive one. The customer experience is important, but how the customer feels about that experience is critical. Few companies design and deliver for positive emotion.
Now, try these three things:

Mark Sanborn, CSP, CPAE, is the president of Sanborn & Associates, Inc., an “idea studio” that seeks to motivate and develop leaders in and outside of business. He’s the best-selling author of books like Fred Factor and The Potential Principle and a noted expert on leadership, team building, customer service and company change. He holds the Certified Speaking Professional designation from the National Speakers Association and is a member of the Speaker Hall of Fame. Check out any of his excellent books, his video series “Team Building: How To Motivate And Manage People” or his website, MarkSanborn.com, to learn more.
About a year ago, we started hearing about new requirements for organizations doing business with the United States Federal Government, particularly with the Department of Defense (DoD). In the interest of protecting sensitive information, the government began developing and introducing the Cybersecurity Maturity Model Certification, or CMMC. While there are many similarities for the goals and framework of CMMC as compared to other standards such as HIPAA/HITECH and PCI, the CMMC adjusted standards in a way that are meaningful and important to discuss..
In this blog you will find out key pieces of information you should know about CMMC so thatyou can meet and maintain strong cybersecurity controls that satisfy the powers that be.
Get the Article Here:

“Should your business be implementing log retention, management, and monitoring for security incidents?”
Products that use event logs generated by various devices to look for potential security incidents are becoming more mainstream. These tools are a combination of log aggregators, which collect the information, AI and security engineers who use this data to identify security incidents as they occur to stop or minimize damage.
These tools are appealing to businesses seeking to limit their security risks, as it should be. Having a designated individual to watch your systems in real time can be a huge risk mitigator. However, these solutions do require some investment that many businesses may be hesitant to make. These solutions aren’t necessarily a good fit for every business.
But who should be looking at this?
Organizations that have significant compliance concerns are often mandated to have log management, retention, and monitoring solutions. Even if your business is not mandated, consider what the consequences would be if you had a significant security incident and/or data breach.
What would the impact be? If you believe this represents an existential threat to your organization, which may often be the case as many organizations do not recover from serious cyber-security incidents, then an investment in these kinds of solutions can have a positive return on investment.